Phishing Emails Found in Environments Protected by Secure Email Gateways (SEGs)
Every week we update this page with a selection of the latest threats our analysts discover in environments protected by Proofpoint and other SEGs. These threat feeds can inform your security teams and help protect your business from malware-bearing phish.
One hundred percent of the phish seen by the Cofense Phishing Defense Center (PDC) have been found in environments under SEG (secure email gateway) protection, were reported by users, and were analyzed and dispositioned by Cofense Triage.
Cofense solutions enable organizations to identify, analyze and quarantine email threats in minutes.
Are phishing emails evading your Proofpoint or other secure email gateway? The following are examples of phishing emails recently seen by the PDC in technology-protected environments.
Malicious emails continue to reach user inboxes, increasing the risk of account compromise, data breach, ransomware attack and more. The same patterns and techniques are used and observed week after week. Get real-world ransomware attack email examples here and learn how to protect yourself.
Filter by SEG
SEG
Tactic
Theme
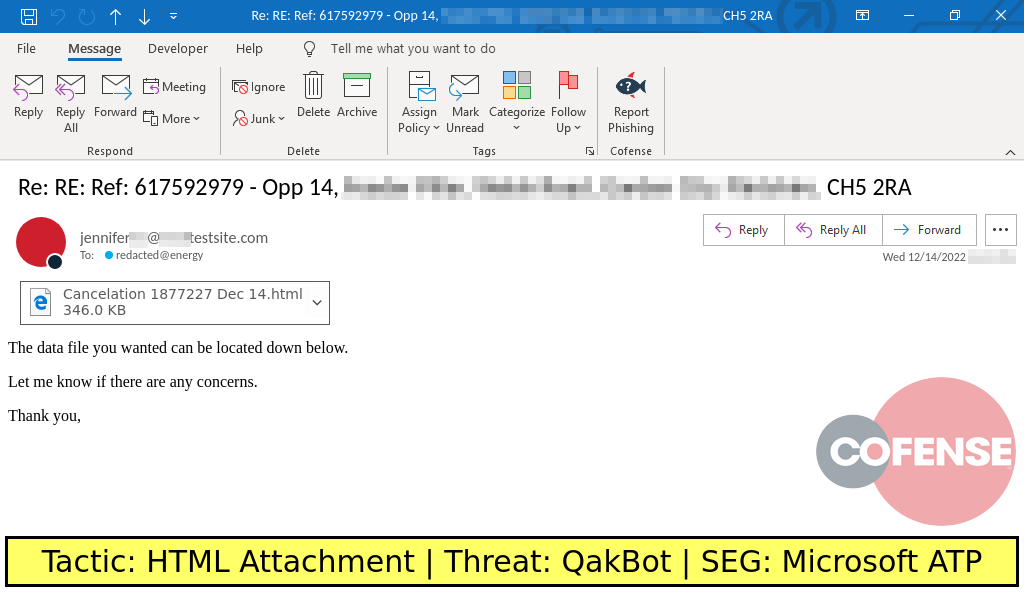
ENVIRONMENTS: Microsoft Defender for O365
TYPE: QakBot
POSTED ON: 12/14/2022
TACTIC: HTML Attachment
THEME: Notification
PHISHING EXAMPLE DESCRIPTION: Notification-themed emails found in environments protected by Microsoft ATP deliver a password protected .zip archive via an attached HTML file. The archive contains an .img file which contain a QakBot .dll and a .lnk file which is used to run the .dll.
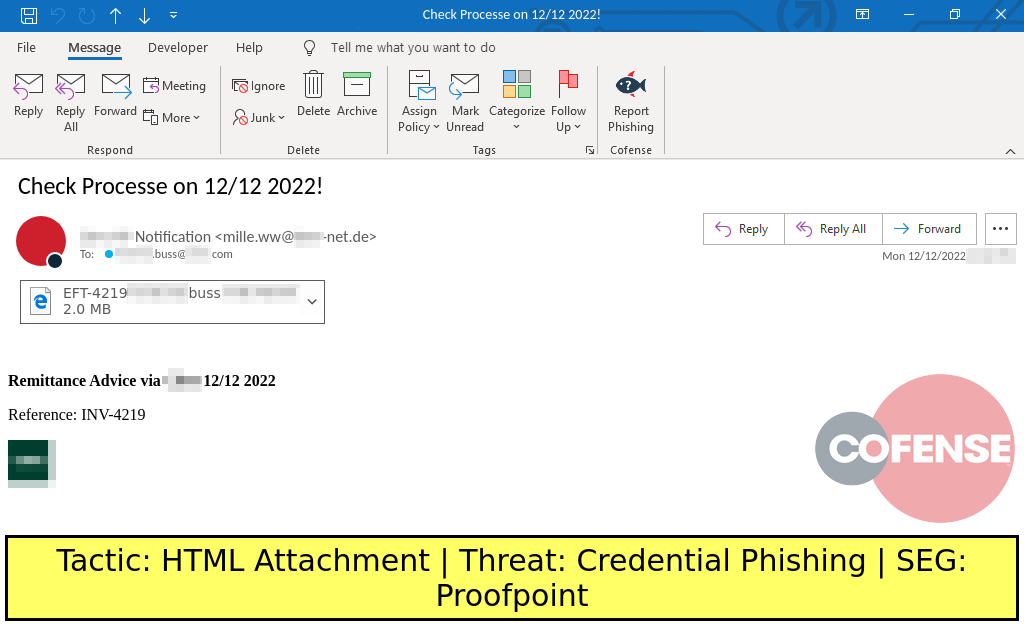
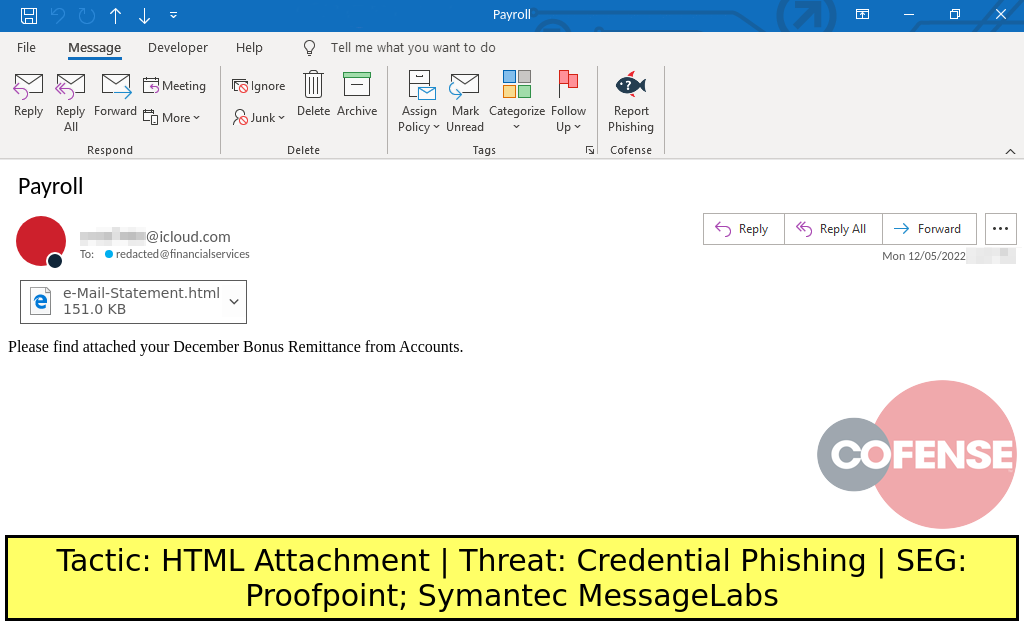
ENVIRONMENTS: Proofpoint
TYPE: Credential Phishing
POSTED ON: 12/12/2022
TACTIC: HTML Attachment
THEME: Finance
PHISHING EXAMPLE DESCRIPTION: Finance-themed emails found in environments protected by Proofpoint deliver Credential Phishing via an HTML attachment.
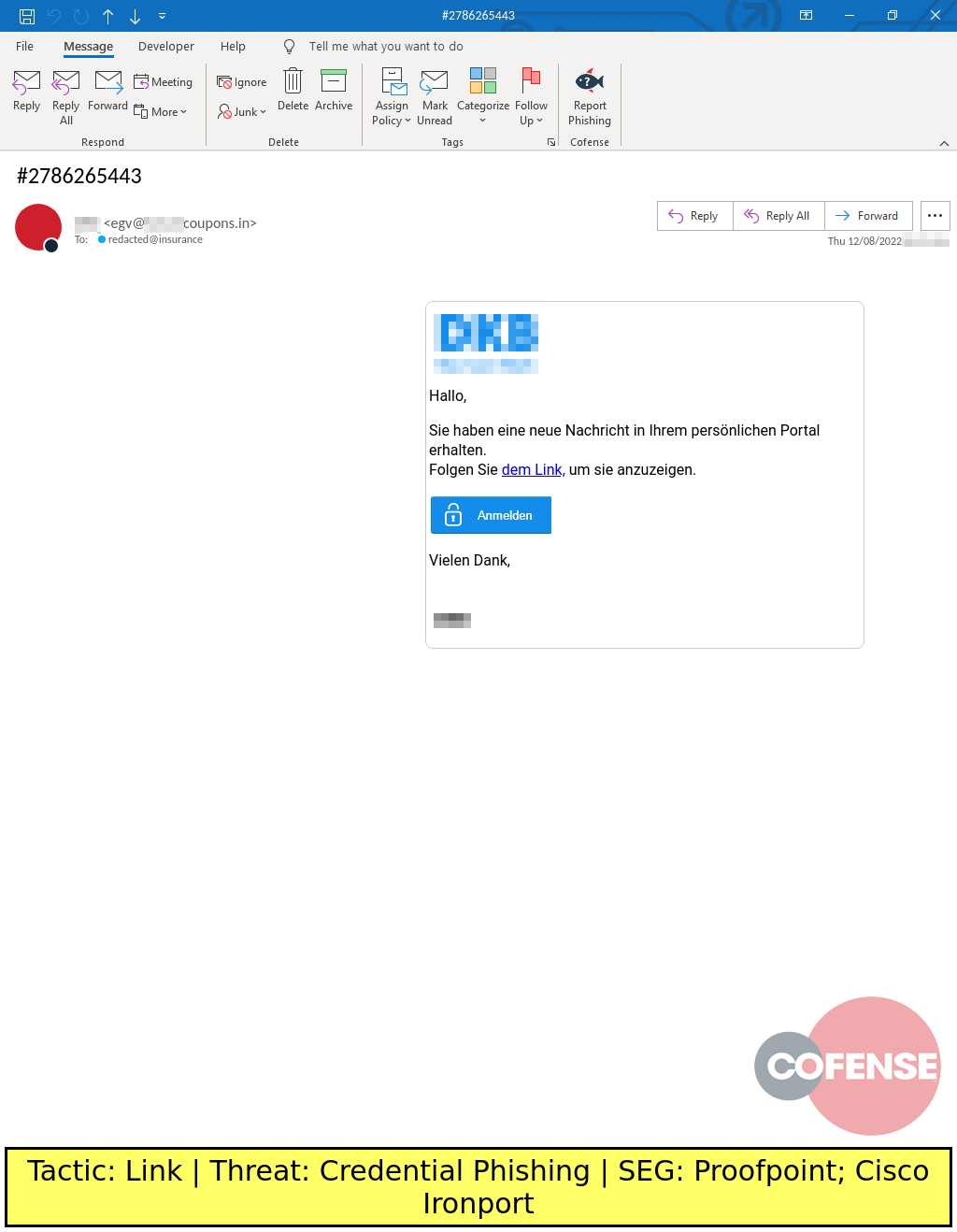
ENVIRONMENTS: Proofpoint
TYPE: Credential Phishing
POSTED ON: 12/08/2022
TACTIC: Link
THEME: DKB-spoofing emails
PHISHING EXAMPLE DESCRIPTION: DKB-spoofing emails found in environments protected by Proofpoint and Cisco Ironport deliver Credential Phishing via an embedded URL.
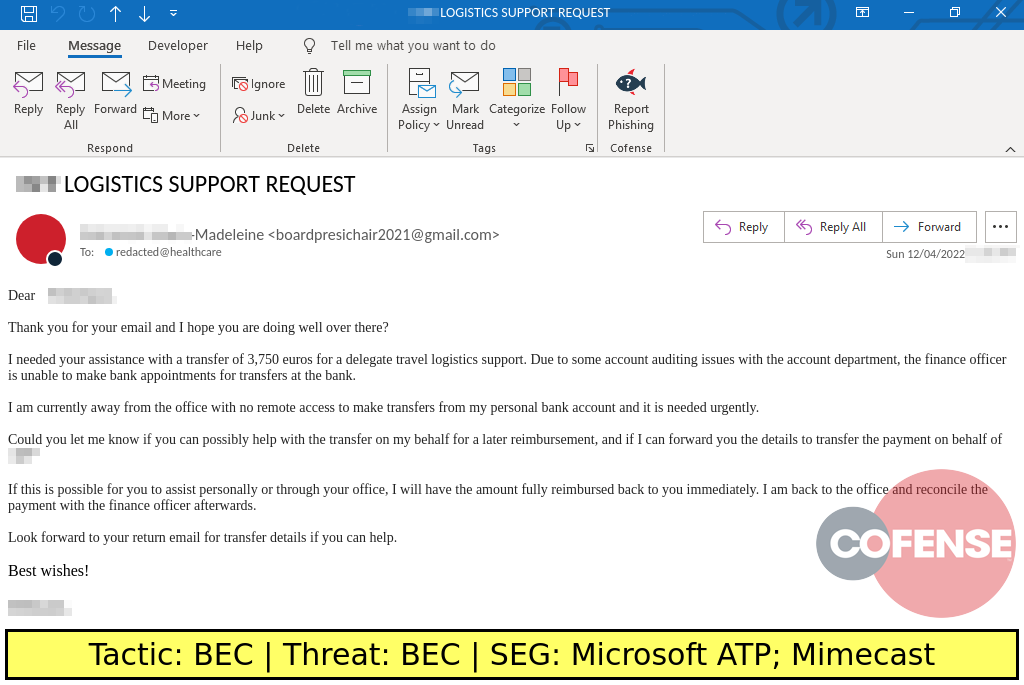
ENVIRONMENTS: Microsoft Defender for O365
TYPE: BEC
POSTED ON: 12/05/2022
TACTIC: BEC
THEME: Finance
PHISHING EXAMPLE DESCRIPTION: Finance-themed emails found in environments protected by Mimecast and Microsoft ATP deliver BEC.
ENVIRONMENTS: Proofpoint
TYPE: Credential Phishing
POSTED ON: 12/05/2022
TACTIC: HTML Attachment
THEME: Finance
PHISHING EXAMPLE DESCRIPTION: Finance-themed emails found in environments protected by Proofpoint and Symantec MessageLabs deliver Credential Phishing embedded in attached HTML files.
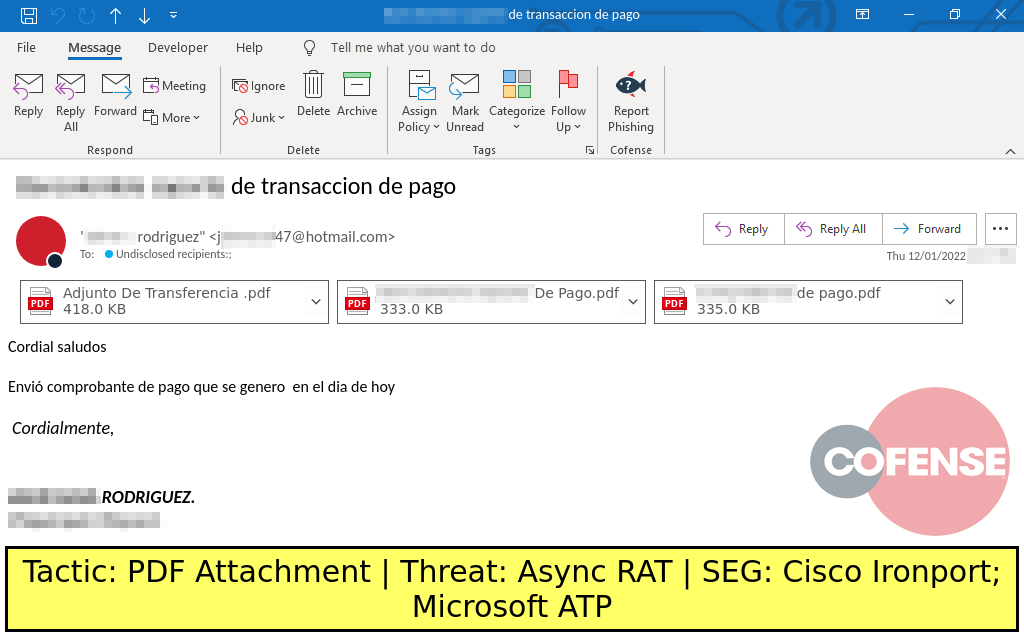
ENVIRONMENTS: Microsoft Defender for O365
TYPE: Async RAT
POSTED ON: 12/01/2022
TACTIC: PDF Attachment
THEME: Finance
PHISHING EXAMPLE DESCRIPTION: Finance-themed emails found in environments protected by Microsoft ATP and Cisco Ironport deliver attached PDF files with links to download password protected archives. The archives contain Async RAT.
Malicious emails continue to reach user inboxes, increasing the risk of account compromise, data breach, ransomware attack and more. The same patterns and techniques are used and observed week after week.
Recommendations
Cofense recommends that organizations train personnel to identify and report suspicious emails and use advanced email protection tools. Cofense PhishMe customers should use SEG Miss templates to raise awareness of these attacks. Organizations should also fortify their cyber response playbook with Cofense Triage and Cofense Vision to quickly analyze and auto quarantine the phishing attacks that bypass technical controls.
Interested in seeing more? Search our real Phishing Database.
All third-party trademarks referenced by Cofense whether in logo form, name form or product form, or otherwise, remain the property of their respective holders, and use of these trademarks in no way indicates any relationship between Cofense and the holders of the trademarks. Any observations contained in this blog regarding circumvention of end point protections are based on observations at a point in time based on a specific set of system configurations. Subsequent updates or different configurations may be effective at stopping these or similar threats.
The Cofense® and PhishMe® names and logos, as well as any other Cofense product or service names or logos displayed on this blog are registered trademarks or trademarks of Cofense Inc.